If you think that the multimedia files that you receive in your complex, encrypted, secure messaging applications cannot be tampered with, you should think again.
Yesterday, Symantec security researchers demonstrated some interesting scenarios of attacks on WhatsApp and Telegram applications for Android, which could allow attackers to spread false news or deceive users when sending payments to incorrect accounts using Media file jacking attack.
Nicknamed “Media File Jacking,” the attack uses the already known fact that any application installed on a device can access and overwrite files stored in external memory, including files saved by other applications installed on the same device.
WhatsApp and Telegram allow users to choose whether they want to save all incoming multimedia files in the internal or external memory of their device.
Also Read: Facebook Is Fined $5 Billion To Settle FTC Privacy Investigation
However, by default, WhatsApp for Android automatically saves media files in external memory, and Telegram for Android uses internal memory to store user files that are not available for other applications.
However, many Telegram users manually change this parameter to external memory using the Save to Gallery option in the settings when they want to share the received multimedia files with their friends using other communication applications such as Gmail, Facebook Messenger or WhatsApp.
It should be noted that the attack is not limited only to WhatsApp and Telegram, but also affects the functionality and privacy of many other Android applications.
How does the Media File Jacking attack work?
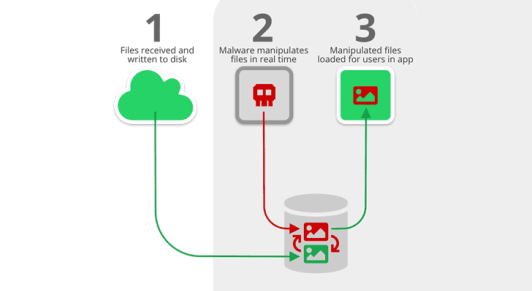
Like man-on-disk attacks, a malicious application installed on the recipient’s device can intercept and process multimedia files, such as personal photos, documents or videos, transferred between users through the device’s external storage, and all this without knowledge receivers and real-time.
“The fact that files are stored and loaded from external memory without adequate security mechanisms allows other applications to authorize recording to external storage to risk the integrity of media files,” the researchers said. blog.
“Attackers can use a trust relationship between the sender and the recipient when they use these instant messaging applications to gain personal gain or damage.”
As shown below, the researchers illustrated and demonstrated four attack scenarios in which a malicious application can instantly analyze and manipulate incoming files, which leads to:
1.) Image manipulation
In this attack scenario, an apparently innocent, but in fact harmful application loaded by the user can be launched in the background to attack the media file, while the victim uses WhatsApp and “manipulates personal photos in almost real-time and without knowing “.
2.) Payment of manipulations
In this scenario, which researchers call “one of the most malicious attacks on media file falsification,” An attacker could manipulate an account sent by a supplier to clients to induce them to make a payment to an account controlled by an attacker.
3.) fake audio messages
In this attack scenario, attackers can use trust relationships between employees of the organization. They can use voice restoration with deep learning technology to change the original sound message for personal gain or for emptying.
4.) Spread false news
In Telegram, administrators use the concept of “channels” to send messages to an unlimited number of subscribers who use published content.
Also Read: More Than 55% Of Email Servers Are Affected By New RCE Vulnerability
With the help of fake multimedia file attacks, an attacker can edit the multimedia files that are displayed in the trusted channels feed in real-time to spread false news.
How to prevent your hackers from breaking into your Android files
Symantec has already notified Telegram and Facebook / WhatsApp about attacks on media storage but believes Google will solve this problem with the next Android Q update.
Android Q includes a new privacy feature called Scoped Storage, which changes the way applications access files in the device’s external memory.
Scoped Storage offers each application an isolated, isolated storage environment in the device’s external memory, where no other application can directly access data stored by other applications on the device.
Prior to this, users can reduce the risk of such attacks by disabling the function responsible for storing media files in the external memory of the device. For this, Android users can upgrade to:
WhatsApp: Settings → Chat → Turn off the “Media Visibility” switch
Telegram: Settings → Chat Settings → Disable the “Save in Gallery” switch



